Home | Solutions Blog | Think Like A Spy
Posts tagged "Think Like A Spy"
 What happens when a spy agency spies on the Congressional body that was created to keep spying in check in the first place? What are the implications of the CIA spying on the Senate?
What happens when a spy agency spies on the Congressional body that was created to keep spying in check in the first place? What are the implications of the CIA spying on the Senate?
That is exactly what Sen. Dianne Feinstein, D-Calif., head of the Senate Intelligence Committee, asserts has happened. In a scathing address to the Senate, Feinstein, who has been a strong advocate of the intelligence community in the past, accused the Central Intelligence Agency (CIA) of violating “the separation of powers principles embodied in the United States Constitution including the Speech and Debate clause”.
This accusation stems from an agreement between the committee and the agency to allow committee aides to review millions of confidential documents related to the post 9/11 Bush administration detention program for handling terror suspects. In the process of reviewing these documents, staffers came across an internal review of the agency’s practices. When the CIA became aware of this, Feinstein claims they searched the network — including the committee’s internal network — and removed the documents.
Posted in Cyber Data Security by Identity Theft Speaker John Sileo.
Tags: Central Intelligence Agency, CIA, Dianne Feinstein, John Sileo, Senate, Senate Intelligence Committee, Sileo, Spying, surveillance, Think Like A Spy

Is there a chance that someone could be stealing your most profitable business secrets? Competitive intelligence isn’t new, but it certainly has gotten easier with the introduction of ubiquitous high resolution cameras (smartphones), miniature storage devices that hold massive amounts of data (USB drives) and advanced tools of human manipulation (social networking).
Dyson, the British engineering firm behind the popular bagless vacuum cleaners and Airblade hand dryers, accused their German counterpart, Bosch, of planting a mole, or corporate spy, inside their headquarters for two years to steal vital research and development information. Bosch has denied any wrongdoing and refuses to return the technology or intellectual property. In an odd twist, Bosch hasn’t publicly denied planting an inside spy to siphon competitive intelligence from their rival.
In a world of highly competitive and rapid technological advancements, this sort of news brings to mind three crucial questions for businesses wanting to protect their intellectual property:
Posted in Digital Reputation & Trust, Fraud Detection & Prevention by Identity Theft Speaker John Sileo.
Tags: "competitive intelligence", "corporate espionage advisor", "corporate espionage expert", "corporate espionage presentation", "corporate espionage speaker", "Inside Job", corporate espionage, espionage, Expert, Fraud Training, John Sileo, Sileo, Think Like A Spy
Privacy Means Profit (Wiley) available in bookstores today!
Here are The Top 5 Reasons You Shouldn’t Buy It:
 You love sharing bank account numbers, surfing habits and customer data with cyber thieves over unprotected wireless networks
You love sharing bank account numbers, surfing habits and customer data with cyber thieves over unprotected wireless networks
 You never tempt hackers and con artists by using Gmail, Facebook, LinkedIn, Twitter, Google Docs, or other cloud computing platforms to store or communicate private info, personally or professionally.
You never tempt hackers and con artists by using Gmail, Facebook, LinkedIn, Twitter, Google Docs, or other cloud computing platforms to store or communicate private info, personally or professionally.
 You bury your head in the sand, insisting that “insider theft” won’t affect your home or business.
You bury your head in the sand, insisting that “insider theft” won’t affect your home or business.
 You’ve already hardened your laptops and other mobile computing devices in 7 vital ways, eliminating a major source of both personal and corporate data theft.
You’ve already hardened your laptops and other mobile computing devices in 7 vital ways, eliminating a major source of both personal and corporate data theft.
 You have a “thing” for identity theft recovery costs and would rather invest thousands in recovery than $25 in prevention.
You have a “thing” for identity theft recovery costs and would rather invest thousands in recovery than $25 in prevention.
If you want to defend yourself and your business against identity theft, data breach and corporate espionage, then buy a copy of Privacy Means Profit.
Posted in Cyber Data Security, Digital Reputation & Trust, Fraud Detection & Prevention, Identity Theft Prevention, Online Privacy by Identity Theft Speaker John Sileo.
Tags: identity theft expert, Identity Theft Prevention, Identity Theft Protection, Identity Theft Speaker, John Sileo, Privacy Means Profit, Think Like A Spy, Wiley, Wiley & Sons
ThinkLikeASpy.com got a makeover!

We recently updated our website dedicated to my day job as a professional identity theft speaker and expert. The re-launch reflects the release of our new book, Privacy Means Profit, updated resources and our recent appearance on 60 Minutes.
We hope the new website will help you stay up to date on current information survival issues like social media exposure, browser espionage, cyber theft and host of other issues.
Feel free to email us with any questions, comments or feedback on the new site.
The New Features include:
Posted in Identity Theft Prevention by Identity Theft Speaker John Sileo.
Tags: identity theft expert, Identity Theft Speaker, Information Survival, Think Like A Spy
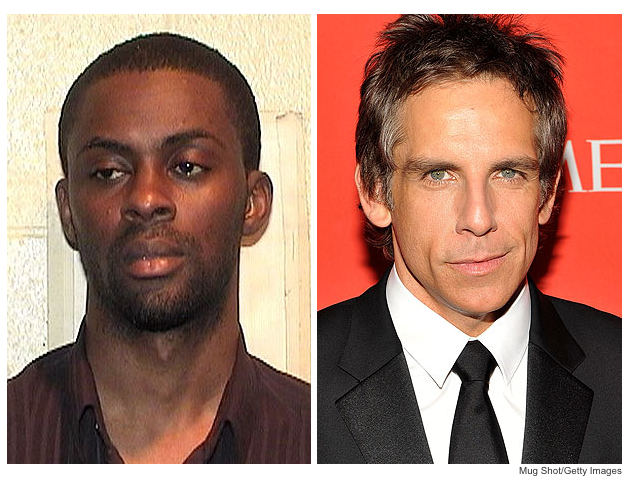
Wouldn’t you think Ben Stiller is famous enough to be immune to losing his identity to a thief? Not so! Credit card scams can bring anyone to their knees, even Hollywood’s most famous!
Many celebrities have recently been the victims of a credit card scam that seems too easy to be true. All it took was the suspect calling the credit card companies using the stars’ personal information, claiming the cards had been lost. He requested the replacement cards be sent to a Chicago address and in a matter of days was able to begin his shopping spree. Eventually, a skeptical undercover agent from the US Postal Inspection Service was able to think like a spy and detect the fraud after he hand-delivered the cards to the suspect.
Now this week Adedamola Olatunji, 29, a Nigerian-born man who allegedly used Stiller’s card to run up charges on iTunes and an on-line dating service, was indicted on forgery, mail fraud, theft, aggravated identity theft, computer fraud and other felony charges.
Posted in Identity Theft Prevention by Identity Theft Speaker John Sileo.
Tags: Ben Stiller, Credit card Scams, identity theft expert, Identity Theft Prevention, Identity Theft Speaker, John Sileo, social engineering, Think Like A Spy
If it seems too good to be true, it probably is. 
That is the best way to Think Like A Spy and be alert of Social Engineers that are trying to manipulate you. With such a gloomy economy and many people without work, offers for fast cash and huge discounts become more and more attractive. Most of these Identity Theft cases use the technique of Social Engineering.
Social Engineering is the act of manipulating people into performing actions or divulging confidential information by playing on their human emotions. The term typically applies to deception for the purpose of information gathering, fraud, or computer system access; in most cases the attacker never comes face-to-face with the victim. These days most thieves can nab your identity over the phone, mail, email, and through social networking sites such as Facebook and Twitter.
Posted in Fraud Detection & Prevention, Identity Theft Prevention, Online Privacy by Identity Theft Speaker John Sileo.
Tags: Facebook, Human Emotions, identity theft expert, Identity Theft Prevention, John Sileo, Online/Social Media Privacy, social engineering, Think Like A Spy, twitter
 What happens when a spy agency spies on the Congressional body that was created to keep spying in check in the first place? What are the implications of the CIA spying on the Senate?
What happens when a spy agency spies on the Congressional body that was created to keep spying in check in the first place? What are the implications of the CIA spying on the Senate?