Home | Expert | Page 7
Posts tagged "Expert"
Victim of a Cyber Attack? What You Should Tell Customers
It seems like every day consumers are learning of data breeches from companies like Sega, Sony and Google. Major corporations like these tend to have the funds and resources to recover from an attack, but for small businesses, that’s often not the case.
A slow response and lack of communication with customers are among the missteps many small businesses make when facing an attack, both of which can cause irreparable damage to the business.
“When consumers are a victim of ID fraud based on interaction with a small business, 1 in 3 never come back,” said Phil Blank, senior analyst for security and fraud at Javelin Strategy & Research.
Posted in Cyber Data Security, Fraud Detection & Prevention, Identity Theft Prevention by Identity Theft Speaker John Sileo.
Tags: Business Fraud, Citibank, Citigroup, Data Breach, Expert, Fox, Identity Theft Prevention, john, PlayStation, Sileo, Sony
This week’s news of the theft of private data comes from Citigroup. Seems that even the most reputable organizations can be exposed to the ever-more frequent data breaches we read about. You’ll likely recall the recent news of Sony, PBS, Epsilon and Lockheed Martin. Regrettably, the list is growing by the day. It affects me, and likely, it affects you. Now what?
First, arm yourself with the facts. See the attached articles.
- http://blogs.wsj.com/deals/2011/06/09/citigroup-data-breach-4-tips-to-protect-yourself/
- http://www.reuters.com/article/2011/06/09/us-citi-idUSTRE7580TM20110609
- http://www.informationweek.com/news/181502068
Second, remember to protect your most important data (this information, on its own, or in any combination, is a jackpot to an identity thief):
- Social Security number
- Date of birth
- PIN
- Credit Card numbers
- Bank Account numbers
- Birthdate
Third, never reply to an e-mail requesting personal information. Unless you originate the communication, suspect the worst and do not respond. This is referred to as “Phishing” and the results are never good.
Posted in Cyber Data Security, Identity Theft Prevention by Identity Theft Speaker John Sileo.
Tags: breach, Citi, Citibank, Citigroup, Credit Cards, Expert, Identity Theft Prevention, John Sileo
I love Canadian accountants because not only are they some of the warmest people I have met (I speak on identity theft quite a bit in Canada), but they are incredibly eager to learn how to avoid some of the data security mistakes that we have made in the U.S. As accountants, they provide a ton of vital financial advice to their clients, and I can easily see them sharing some of the data security best practices I talked about during the presentation and getting paid well by their clients to do it. And here’s how I could tell their level of absorption: after the speech, they had a slew of detailed follow-up questions. They were curious. You can always tell someone’s intention to act and make changes by their clarification questions. No questions, no interest, no intent to act. Definitely not what I experienced in the charming town of Winnipeg.
Posted in Identity Theft Prevention, Video Tips by Identity Theft Speaker John Sileo.
Tags: Accountants, Canada, Expert, ICAM, Identity Theft Prevention, Institute of Canadian Accountants, John Sileo, Manitoba, Speaker
We’ve all done it before – left the table to get a coffee refill or go to the bathroom and left our laptop, iPad, smartphone or purse sitting on the table. We justify it by telling ourselves that we are in a friendly place and will only be gone a second. Our tendency is to blame technology for information theft, but the heart of the problem is almost always a human error, like leaving our devices unattended. Realizing that carelessness is the source of most laptop theft makes it a fairly easy problem to solve.
My office is directly above a Starbucks, so I spend way too much time there. And EVERY time I’m there, I watch someone head off to the restroom (see video) or refill their coffee and leave their laptop, iPad, iPhone, briefcase, purse, client files and just about everything else lying around on their table like a self-service gadget buffet for criminals and opportunists alike.
Posted in Burning Questions (Video), Cyber Data Security, Fraud Detection & Prevention, Identity Theft Prevention, Video Tips by Identity Theft Speaker John Sileo.
Tags: data, data security, Digital, Expert, Identity Theft Prevention, information, ipad, iPhone, IT Department, John Sileo, laptop, protect, Security, Smartphone, Speaker, Starbucks, Theft
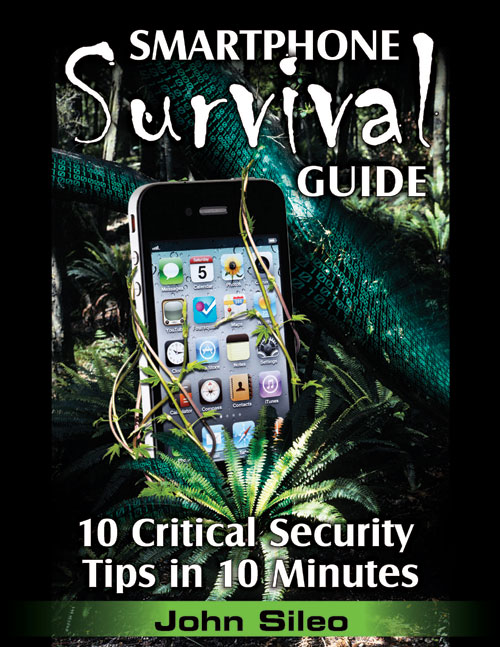
Identity Theft Expert John Sileo has partnered with Amazon.com for a limited time to offer the Smartphone Survival Guide for Kindle at 1/4 of the retail price.
Click Here to Order Today!
The Smartphone Survival Guide: 10 Critical Tips in 10 Minutes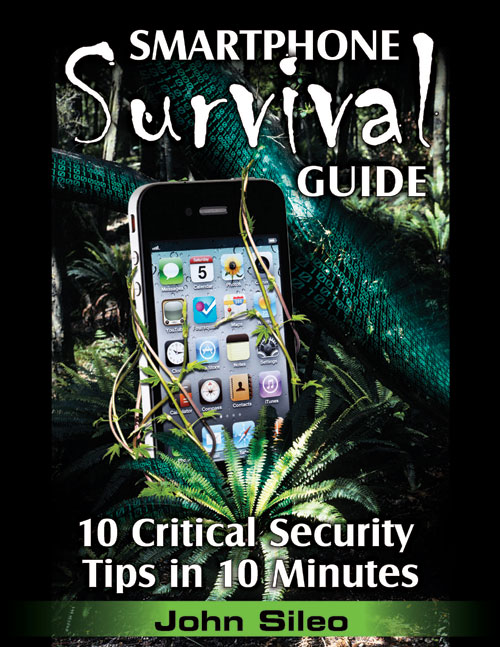
Smartphones are the next wave of data hijacking. Let this Survival Guide help you defend yourself before it’s too late.
Smartphones are quickly becoming the fashionable (and simplest) way for thieves to steal private data. Case in point: Google was recently forced to remove 21 popular Android apps from its official application website, Android Market, because the applications were built to look like useful software but acted like electronic wiretaps. At first glance, apps like Chess appear to be legitimate, but when installed, turn into a data-hijacking machine that siphons private information back to the developer.
Posted in Identity Theft Prevention by Identity Theft Speaker John Sileo.
Tags: Android, Android Market, App Store, Applications, Apps, BlackBerry, BlackBerry Security, data security, Droid, Droid Security, Expert, Fraud, Hacking, Hijacking, iPhone, iPhone Security, jail break, jail breaking, Jailbreaking, John Sileo, Lookout, Mobile Phone, safety, Security, Smart Phone, Smartphone, Smartphone Survival Guide
How should my business balance the risks of social media with the rewards of this increasingly dominant and highly profitable marketing medium? That’s the very insightful question that a CEO asked me during a presentation I gave on information leadership for a Vistage CEO conference.
Think of your move into social media (Facebook/Fan/Business Pages, LinkedIn, Twitter, YouTube, etc.) like you would approach the task of helping your fifteen-year-old daughter prepare to drive on her own. You love her more than anything on earth and would do anything for her (just like you will go to great lengths grow your business), but that doesn’t mean you just hand her the keys. Trying to forbid or ignore the movement into social marketing is like telling your teen that they can’t get their license. It isn’t going to happen, so you might consider putting down the denial and controlling those pieces of change that are within your power. The task is to maximize the positives of her newly bestowed freedom while minimizing any negatives; the same is true in social media.
Posted in Fraud Detection & Prevention, Identity Theft Prevention, Online Privacy by Identity Theft Speaker John Sileo.
Tags: Business Fraud, data security, Expert, Facebook, Facebook Risks, John Sileo, linkedin, Online/Social Media Privacy, Privacy, safety, Security, Social Media Business, social networking, Social Networking Business, Social Networking Risks, Speaker, twitter, YouTube
With the recent avalanche of digital convenience and mass centralization comes our next greatest privacy threat – the stupid use of Mobile Apps. As a society, we depend on the latest technology and instant connectivity so desperately that we rarely take the time to vet the application software (Apps) we install on our mobile phones (and with the introduction of the Mac App store, on our Macs). But many of the Apps out there have not been time-tested like the software on our computers. As much as we love to bash Microsoft and Adobe, they do have a track record of patching security concerns.
The ability to have all of your information at your fingertips on one device is breathtakingly convenient. My iPhone, for example, is used daily as an email client, web browser, book, radio, iPod, compass, recording device, address book, word processor, blog editor, calculator, camera, high-definition video recorder, to-do list, GPS, map, remote control, contact manager, Facebook client, backup device, digital filing cabinet, travel agent, newsreader and phone… among others (which is why I minimize my stupidity by following the steps I set out in the Smart Phone Survival Guide).
Posted in Cyber Data Security, Identity Theft Prevention by Identity Theft Speaker John Sileo.
Tags: Android, Applications, Apps, BlackBerry, data security, Droid, Expert, Fraud, Hacking, iPhone, jail break, jail breaking, Jailbreaking, John Sileo, Mobile Phone, safety, Security, Smart Phone, Smartphone, Smartphone Survival Guide
In response to the increasing data theft threat posed by Smartphones, identity theft expert John Sileo has released The Smartphone Survival Guide. Because of their mobility and computing power, smartphones are the next wave of data hijacking. iPhone, BlackBerry and Droid users carry so much sensitive data on their phones, and because they are so easily compromised, it’s disastrous when they fall into the wrong hands.
Denver, CO (PRWEB) March 7, 2011
Smartphones are quickly becoming the fashionable (and simplest) way for thieves to steal private data. Case in point: Google was recently forced to remove 21 popular Android apps from it’s official application website, Android Market, because the applications were built to look like useful software but acted like electronic wiretaps. At first glance, apps like Chess appear to be legitimate, but when installed, turn into a data-hijacking machine that siphons private information back to the developer.
Posted in Cyber Data Security, Fraud Detection & Prevention, Identity Theft Prevention by Identity Theft Speaker John Sileo.
Tags: Android, Android Market, App Store, Applications, Apps, BlackBerry, BlackBerry Security, data security, Droid, Droid Security, Expert, Fraud, Hacking, Hijacking, iPhone, iPhone Security, jail break, jail breaking, Jailbreaking, John Sileo, Lookout, Mobile Phone, safety, Security, Smart Phone, Smartphone, Smartphone Survival Guide
Google removes 20+ Apps from Android Market, signaling that malware distribution has gone mainstream, and not just for Droids.
The Adroid Operating System is open source – meaning that anyone can create applications without Google’s approval. It boosts innovation, and unlike Apple iPhones or Blackberrys, Droid Apps aren’t bound by all of the rules surrounding the Apple App Store. But this leniency can be exploited by hackers, advertisers and malicious apps. And now those apps aren’t just available on some sketchy off-market website, but on the Android Market itself. As smartphones and tablets become one of the primary ways we conduct business, including banking, this development shifts the security conversation into high gear.
A recent discovery forced Google to pull 21 popular and free apps from the Android Market. According to the company, the apps are malware and focused on getting root access to the user’s device (giving them more control over your phone than even you have). Kevin Mahaffey, the CTO of Lookout, a maker of security tools for mobile devices, explained the Android malware discovery in a recent PC World article (emphasis mine):
Posted in Cyber Data Security, Identity Theft Prevention by Identity Theft Speaker John Sileo.
Tags: Android, Android Market, App Store, Applications, Apps, BlackBerry, BlackBerry Security, data security, Droid, Droid Security, Expert, Fraud, Hacking, Hijacking, iPhone, iPhone Security, jail break, jail breaking, Jailbreaking, John Sileo, Lookout, Mobile Phone, safety, Security, Smart Phone, Smartphone, Smartphone Survival Guide