Home | Cyber Data Security | Page 7
Latest "Cyber Data Security" Posts
[youtube http://www.youtube.com/watch?v=w2oxGBSDW9E&ns?rel=0]
The story about the Texas parents who were terrified when their child’s video baby monitor was hacked struck me at first as a minor incident when viewed in the whole scheme of the world of hackers. After all, it is a rare event, no one was hurt, no threats were overtly made, and the child herself even slept through the event. But when I read more about it, I became increasingly bothered by the fact that I was not initially bothered by it! I mean, is that the creepiest of all feelings, to know that a stranger is watching your kids?
Posted in Cyber Data Security, Sileo In the News by Identity Theft Speaker John Sileo.
Tags: “security breach”, Expert, Hacking, identity theft expert, John Sileo, Sileo, Speaker

Mobile Security Webinar: Defending the Devices that Power Your Productivity
Admit it. You compute almost as much on mobile devices as you do on your main computer. You are hyper efficient because you are always connected. You read work emails on your iPhone or Droid, log in to sensitive Internet accounts via iPad and store mission critical files on your laptop. Thanks to the independence, flexibility and efficiency afforded by mobile gadgets, desktop computing is quickly becoming an outdated notion. To remain nimble and relevant, you must be able to connect, communicate and compute from anywhere.

But along with the rewards of freedom, mobile computing also comes with risk. Small devices are easier to lose, simple to steal and targets for data theft. Here’s the good news: Deluxe can help you stay one step ahead of the hackers, competitors and criminals looking to use your data to drive their profits.
Posted in Cyber Data Security, Identity Theft Prevention by Identity Theft Speaker John Sileo.
Tags: Deluxe, Expert, John Sileo, Mobile, mobile data, Mobile Security, Sileo, Speaker
NSA Surveillance includes the collection of your phone and email records for the sake of detecting and disrupting terrorism. The practice has proven effective, but the scope of the data collected (every phone call and email available, even if you are innocent) has raised eyebrows.
Congress, in a rare show of bipartisan agreement, may be leaning toward limiting the amount of data the NSA can collect.
Rep. Justin Amash, R-Mich., backed by Rep. John Conyers, D-Mich., put forth an amendment that would restrict the NSA’s ability to collect data under the Patriot Act on people not connected to an ongoing investigation. The action was initiated after Edward Snowden, a government contract worker, leaked highly classified data to the media, revealing that the NSA has secretly collected phone and email records on millions of Americans without their knowledge or consent.
Posted in Cyber Data Security, Identity Theft Prevention by Identity Theft Speaker John Sileo.
Tags: Cyber Security, Cyber Security Expert, Cyber Security Keynote Speaker, Cyber Security Speaker, Cybersecurity, Digital Surveillance, John Sileo, National Security Administration, NSA Surveillance, Patriot Act, PRISM
Google Glass Privacy
When Google released a trial version of its much-anticipated and much-hyped Augmented Reality lens (popularly known as Google Glass) to developers back in April, I wrote a blog on Google Glass Privacy. Now is a good time to check in and see what’s happened since the glasses have fallen into the hands of developers. By developers, I mean hackers (many of them of the good, or white-hat variety). Google gave Google Glasses to 1500 developer/hackers (well, sold them-for $1,500 to those who won an essay-based lottery). Brilliant move really, because these people are showing Google (and us, and future hackers) exactly what can, and will, happen when the mainstream public gets their hands on it. Here are some of the unintended uses of Google Glass:
Posted in Cyber Data Security, Online Privacy by Identity Theft Speaker John Sileo.
Definitions
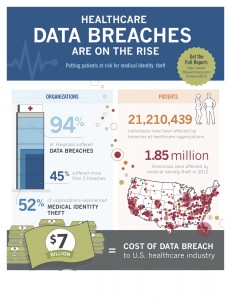
Identity Theft: involves the misuse of another individual’s personal identifiable information for fraudulent purposes.
- Identity theft is the fastest-growing crime in the U.S., affecting 1 in 20 consumers.
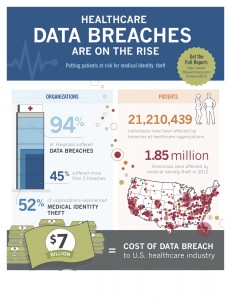
Medical Identity Theft: occurs when someone uses an individual’s name and personal identity to fraudulently receive medical services, prescription drugs or goods, including attempts to commit fraudulent billing.
- Medical identity theft affected 2 million people in the U.S. in 2011.
Data Breach: a security incident in which sensitive, protected or confidential data is copied, transmitted, viewed, stolen or used by an unauthorized individual. Data Breaches may involve:
- Credit card numbers
- Personally identifiable information
- Protected health information
- Social Security Number
- Trade secrets
- Intellectual property
Who/What’s at Stake?
An identity is stolen every 3 seconds!
- 5 million Americans were victims of identity theft in 2003.
Posted in Cyber Data Security, Identity Theft Prevention by Identity Theft Speaker John Sileo.
Tags: “data breaches”, cyberterrorism, Data Breach, Expert, ID Experts, identity theft expert, John Sileo, Sileo, Speaker
And in the latest installment of “breaking news” that shouldn’t surprise you at all…
…FBI Director Robert S. Mueller III admitted that the United States has used drones over US airspace. It was the first time an FBI official publicly admitted such a program exists, but if you want to believe pop culture (the latest Bourne installment, a recent Castle episode, the Call of Duty video game), drone use is more common than we think.
What we know:
- Drones (or unmanned, remotely piloted aircraft) have been used since the early 1900s, for various purposes, primarily military and law enforcement, though there are increasing demands for public use.
- The Drug Enforcement Agency and the Bureau of Alcohol, Tobacco, Firearms and Explosives have both tested drones for use in investigations.
- The Federal Aviation Administration has to approve all drone use in US airspace.
Posted in Cyber Data Security, Sileo In the News by Identity Theft Speaker John Sileo.
Tags: Drones, Expert, FBI, Privacy, Sileo, surveillance
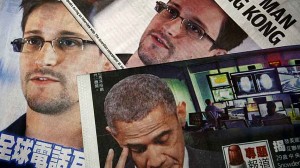
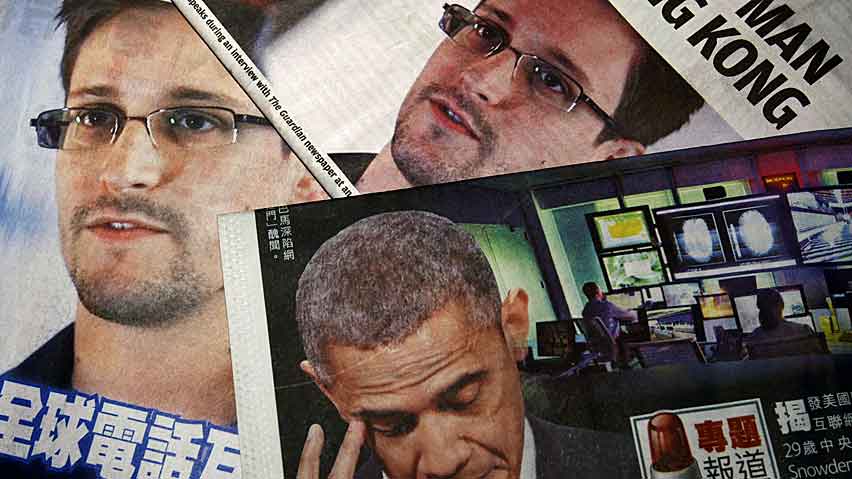
I’m in the business of encouraging people to keep their guard up. I’m always telling people to watch for signs of something that doesn’t feel quite right, take precautionary measures, and stay informed. But even I have to question the tactics some are recommending when it comes to reacting to the NSA PRISM surveillance program leaked by Edward Snowden. In a previous post on this topic, I said it isn’t a black or white argument, but some people are asking you to make it one.
Best-selling author, technology expert and Columbia Law School professor, Tim Wu, has said that web users have a responsibility to quit Internet companies like Google, Facebook, Apple, Yahoo and Skype if it is indeed verified that they have been collaborating with the NSA. In fact, Wu bluntly proclaimed, “Quit Facebook and use another search engine. It’s simple. It’s nice to keep in touch with your friends. But I think if you find out if it’s true that these companies are involved in these surveillance programs you should just quit.” Wu acknowledged that there is still much to learn about this program and admitted it was no surprise that PRISM exists, saying, “When you have enormous concentrations of data in a few hands, spying becomes very easy.”
Posted in Cyber Data Security, Online Privacy, Sileo In the News, Uncategorized by Identity Theft Speaker John Sileo.
Tags: Expert, NSA, PRISM, Privacy, Sileo, Snowden, surveillance
When you log onto the Verizon Precision Market Insights website, the giant catch phrase that jumps out at you in bold red letters is:
“Know your audience more precisely.
Drive your business more effectively.”
Verizon is pulling no punches when it comes to letting advertisers know that they have valuable data- OUR data- and they’re willing to share it. For a price of course. Phone carriers, who see a continued decline in contract subscriber growth and voice calls, are hoping to generate new sources of revenue by selling the data they collect about us. They already collect information about user location and Web surfing and application use (which informs them about such things as travels, interests and demographics) to adjust their networks to handle traffic better. Now they have begun to sell this data.
Posted in Cyber Data Security, Identity Theft Prevention, Online Privacy, Uncategorized by Identity Theft Speaker John Sileo.
Tags: AT&T, Big Data, Expert, opt out, Phone Surveillance, Privacy, Sileo, Sprint, surveillance, T-Mobile, Verizon, Wire Tapping
Do you value national security? Do you want to live free of fear from random terrorist acts like the Boston Marathon bombing? Do you value your privacy? Should you be allowed to act in legal ways without others (namely, the government) digitally eavesdropping on your secrets?
A former data spy is asking us to decide where we stand on the spectrum separating security and privacy. Edward Snowden, 29, a former contractor to the National Security Agency (the guys and gals in charge of wire-tapping phones and internet traffic) and an employee of the CIA, leaked classified documents to reporters about two far-reaching U.S. surveillance programs. Fearing government reprisal, Snowden is hiding in Hong Kong, a country he believes has “a spirited commitment to free speech and the right of political dissent”.
Posted in Cyber Data Security, Online Privacy by Identity Theft Speaker John Sileo.
Tags: Expert, NSA, Privacy, Sileo, Snowden, surveillance