Home | Solutions Blog | Apps
Posts tagged "Apps"
 You and I have come to think of our Smartphones as indispensable tools. Flaws recently discovered in mobile apps for Facebook, Linkedin and Dropbox could turn our tools into weapons by exposing us to data theft at many levels, including personal identity theft and corporate data loss.
You and I have come to think of our Smartphones as indispensable tools. Flaws recently discovered in mobile apps for Facebook, Linkedin and Dropbox could turn our tools into weapons by exposing us to data theft at many levels, including personal identity theft and corporate data loss.
Taking extra precautions now will protect not only your Smartphone but other devices, too, as the flaw may well be present in other mobile applications including many iOS games.
Apparently, Facebook’s iOS and Android apps don’t encrypt their users’ login credentials. These flaws expose users to identity theft by saving user authentication keys (usernames and passwords) in easily accessible, plain text files. These unencrypted files may be stolen, transferred to another device in a matter of minutes, and used to access the victim’s accounts without ever having to enter any user login credentials.
Posted in Cyber Data Security, Fraud Detection & Prevention, Identity Theft Prevention by Identity Theft Speaker John Sileo.
Tags: Android, Applications, Apps, data security, encryption, Expert, iOS, iPhone, John Sileo, Mobile, Mobile Apps, Mobile Security, Privacy, Security, Smart Phone, Smartphone, Speaker
Identity Theft Expert John Sileo has partnered with Amazon.com for a limited time to offer the Smartphone Survival Guide for Kindle at 1/4 of the retail price.
Click Here to Order Today!
The Smartphone Survival Guide: 10 Critical Tips in 10 Minutes
Smartphones are the next wave of data hijacking. Let this Survival Guide help you defend yourself before it’s too late.
Smartphones are quickly becoming the fashionable (and simplest) way for thieves to steal private data. Case in point: Google was recently forced to remove 21 popular Android apps from its official application website, Android Market, because the applications were built to look like useful software but acted like electronic wiretaps. At first glance, apps like Chess appear to be legitimate, but when installed, turn into a data-hijacking machine that siphons private information back to the developer.
Posted in Identity Theft Prevention by Identity Theft Speaker John Sileo.
Tags: Android, Android Market, App Store, Applications, Apps, BlackBerry, BlackBerry Security, data security, Droid, Droid Security, Expert, Fraud, Hacking, Hijacking, iPhone, iPhone Security, jail break, jail breaking, Jailbreaking, John Sileo, Lookout, Mobile Phone, safety, Security, Smart Phone, Smartphone, Smartphone Survival Guide
The identity theft and corporate data risk problem isn’t limited to iPad users – it affects all Tablets – but iPads are leading the way. With the rapid increase in highly powerful tablet computers, including the Motorola Xoon and Samsung Galaxy, a new survey is urging users to beware of the risks. Harris Interactive just released a study showing that tablet users transmit more sensitive information than they do on smartphones and are considerably less confident of the security protecting those tablets.
The survey shows that 48% of tablet users transfer sensitive data using the device while only 30% of smart phone users transfer sensitive information. The types of sensitive data included credit card, financial, personal and even proprietary business information. Many factors contribute to the increased risk:
- Users initially bought tablets as book readers and web browsers, but have increasingly added to their functionality with new Apps.
Posted in Cyber Data Security, Fraud Detection & Prevention, Identity Theft Prevention by Identity Theft Speaker John Sileo.
Tags: Apple, Apps, Data Breach, galaxy, Identity Theft Prevention, ipad, malware, Security, Sileo, tablet, xoon
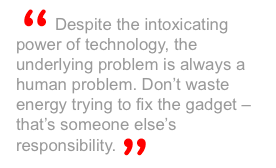
With the recent avalanche of digital convenience and mass centralization comes our next greatest privacy threat – the stupid use of Mobile Apps. As a society, we depend on the latest technology and instant connectivity so desperately that we rarely take the time to vet the application software (Apps) we install on our mobile phones (and with the introduction of the Mac App store, on our Macs). But many of the Apps out there have not been time-tested like the software on our computers. As much as we love to bash Microsoft and Adobe, they do have a track record of patching security concerns.
The ability to have all of your information at your fingertips on one device is breathtakingly convenient. My iPhone, for example, is used daily as an email client, web browser, book, radio, iPod, compass, recording device, address book, word processor, blog editor, calculator, camera, high-definition video recorder, to-do list, GPS, map, remote control, contact manager, Facebook client, backup device, digital filing cabinet, travel agent, newsreader and phone… among others (which is why I minimize my stupidity by following the steps I set out in the Smart Phone Survival Guide).
Posted in Cyber Data Security, Identity Theft Prevention by Identity Theft Speaker John Sileo.
Tags: Android, Applications, Apps, BlackBerry, data security, Droid, Expert, Fraud, Hacking, iPhone, jail break, jail breaking, Jailbreaking, John Sileo, Mobile Phone, safety, Security, Smart Phone, Smartphone, Smartphone Survival Guide
In response to the increasing data theft threat posed by Smartphones, identity theft expert John Sileo has released The Smartphone Survival Guide. Because of their mobility and computing power, smartphones are the next wave of data hijacking. iPhone, BlackBerry and Droid users carry so much sensitive data on their phones, and because they are so easily compromised, it’s disastrous when they fall into the wrong hands.
Denver, CO (PRWEB) March 7, 2011
Smartphones are quickly becoming the fashionable (and simplest) way for thieves to steal private data. Case in point: Google was recently forced to remove 21 popular Android apps from it’s official application website, Android Market, because the applications were built to look like useful software but acted like electronic wiretaps. At first glance, apps like Chess appear to be legitimate, but when installed, turn into a data-hijacking machine that siphons private information back to the developer.
Posted in Cyber Data Security, Fraud Detection & Prevention, Identity Theft Prevention by Identity Theft Speaker John Sileo.
Tags: Android, Android Market, App Store, Applications, Apps, BlackBerry, BlackBerry Security, data security, Droid, Droid Security, Expert, Fraud, Hacking, Hijacking, iPhone, iPhone Security, jail break, jail breaking, Jailbreaking, John Sileo, Lookout, Mobile Phone, safety, Security, Smart Phone, Smartphone, Smartphone Survival Guide
Google removes 20+ Apps from Android Market, signaling that malware distribution has gone mainstream, and not just for Droids.
The Adroid Operating System is open source – meaning that anyone can create applications without Google’s approval. It boosts innovation, and unlike Apple iPhones or Blackberrys, Droid Apps aren’t bound by all of the rules surrounding the Apple App Store. But this leniency can be exploited by hackers, advertisers and malicious apps. And now those apps aren’t just available on some sketchy off-market website, but on the Android Market itself. As smartphones and tablets become one of the primary ways we conduct business, including banking, this development shifts the security conversation into high gear.
A recent discovery forced Google to pull 21 popular and free apps from the Android Market. According to the company, the apps are malware and focused on getting root access to the user’s device (giving them more control over your phone than even you have). Kevin Mahaffey, the CTO of Lookout, a maker of security tools for mobile devices, explained the Android malware discovery in a recent PC World article (emphasis mine):
Posted in Cyber Data Security, Identity Theft Prevention by Identity Theft Speaker John Sileo.
Tags: Android, Android Market, App Store, Applications, Apps, BlackBerry, BlackBerry Security, data security, Droid, Droid Security, Expert, Fraud, Hacking, Hijacking, iPhone, iPhone Security, jail break, jail breaking, Jailbreaking, John Sileo, Lookout, Mobile Phone, safety, Security, Smart Phone, Smartphone, Smartphone Survival Guide
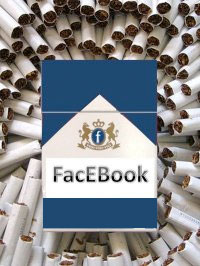
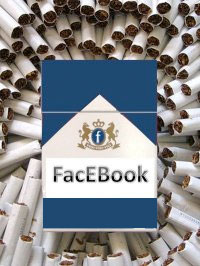 Facebook is a cigarette, information is the nicotine, and you are the addict. And it is time to stop blaming Facebook if you get privacy cancer.
Facebook is a cigarette, information is the nicotine, and you are the addict. And it is time to stop blaming Facebook if you get privacy cancer.
Years ago, after a long and drawn out fight, the tobacco industry was forced to put labels on their cigarette packs warning smokers that these nicotine delivery devices caused cancer, birth defects and premature death. The warnings did little to slow down sales of cigarettes, though they might have helped the tobacco companies avoid some costly lawsuits because, after all, they had clearly warned users about the dangers.
With the latest iteration of privacy settings being introduced this week on Facebook, Mark Zuckerberg (or more likely the brilliant Chief Operating Officer Sheryl Sandberg) has discovered a similar truth – you are either too addicted to the information drug, or too indifferent to the privacy consequences, to care.
Posted in Online Privacy by Identity Theft Speaker John Sileo.
Tags: Addiction, Application, Applications, Apps, Facebook, Groups, Information Addiction, Information Survival, John Sileo, Privacy, Sheryl Sandberg, Third-Party
 You and I have come to think of our Smartphones as indispensable tools. Flaws recently discovered in mobile apps for Facebook, Linkedin and Dropbox could turn our tools into weapons by exposing us to data theft at many levels, including personal identity theft and corporate data loss.
You and I have come to think of our Smartphones as indispensable tools. Flaws recently discovered in mobile apps for Facebook, Linkedin and Dropbox could turn our tools into weapons by exposing us to data theft at many levels, including personal identity theft and corporate data loss.