Home | Solutions Blog | BlackBerry Security
Posts tagged "BlackBerry Security"
Identity Theft Expert John Sileo has partnered with Amazon.com for a limited time to offer the Smartphone Survival Guide for Kindle at 1/4 of the retail price.
Click Here to Order Today!
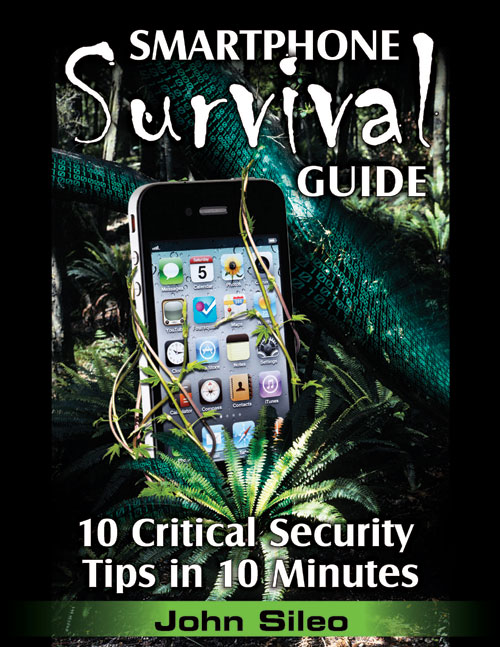
The Smartphone Survival Guide: 10 Critical Tips in 10 Minutes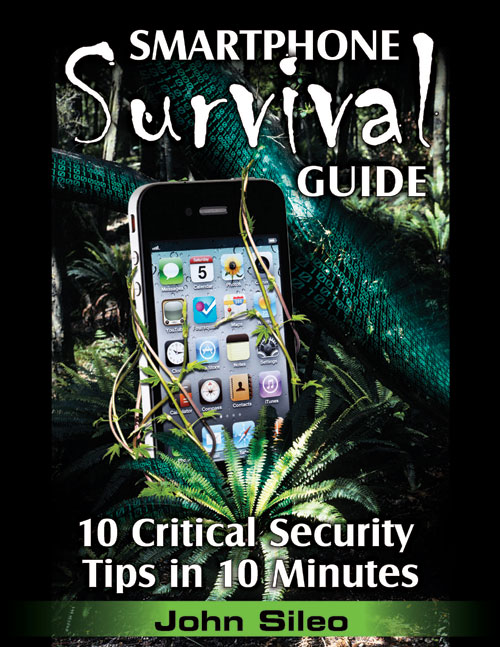
Smartphones are the next wave of data hijacking. Let this Survival Guide help you defend yourself before it’s too late.
Smartphones are quickly becoming the fashionable (and simplest) way for thieves to steal private data. Case in point: Google was recently forced to remove 21 popular Android apps from its official application website, Android Market, because the applications were built to look like useful software but acted like electronic wiretaps. At first glance, apps like Chess appear to be legitimate, but when installed, turn into a data-hijacking machine that siphons private information back to the developer.
Posted in Identity Theft Prevention by Identity Theft Speaker John Sileo.
Tags: Android, Android Market, App Store, Applications, Apps, BlackBerry, BlackBerry Security, data security, Droid, Droid Security, Expert, Fraud, Hacking, Hijacking, iPhone, iPhone Security, jail break, jail breaking, Jailbreaking, John Sileo, Lookout, Mobile Phone, safety, Security, Smart Phone, Smartphone, Smartphone Survival Guide
In response to the increasing data theft threat posed by Smartphones, identity theft expert John Sileo has released The Smartphone Survival Guide. Because of their mobility and computing power, smartphones are the next wave of data hijacking. iPhone, BlackBerry and Droid users carry so much sensitive data on their phones, and because they are so easily compromised, it’s disastrous when they fall into the wrong hands.
Denver, CO (PRWEB) March 7, 2011
Smartphones are quickly becoming the fashionable (and simplest) way for thieves to steal private data. Case in point: Google was recently forced to remove 21 popular Android apps from it’s official application website, Android Market, because the applications were built to look like useful software but acted like electronic wiretaps. At first glance, apps like Chess appear to be legitimate, but when installed, turn into a data-hijacking machine that siphons private information back to the developer.
Posted in Cyber Data Security, Fraud Detection & Prevention, Identity Theft Prevention by Identity Theft Speaker John Sileo.
Tags: Android, Android Market, App Store, Applications, Apps, BlackBerry, BlackBerry Security, data security, Droid, Droid Security, Expert, Fraud, Hacking, Hijacking, iPhone, iPhone Security, jail break, jail breaking, Jailbreaking, John Sileo, Lookout, Mobile Phone, safety, Security, Smart Phone, Smartphone, Smartphone Survival Guide
Google removes 20+ Apps from Android Market, signaling that malware distribution has gone mainstream, and not just for Droids.
The Adroid Operating System is open source – meaning that anyone can create applications without Google’s approval. It boosts innovation, and unlike Apple iPhones or Blackberrys, Droid Apps aren’t bound by all of the rules surrounding the Apple App Store. But this leniency can be exploited by hackers, advertisers and malicious apps. And now those apps aren’t just available on some sketchy off-market website, but on the Android Market itself. As smartphones and tablets become one of the primary ways we conduct business, including banking, this development shifts the security conversation into high gear.
A recent discovery forced Google to pull 21 popular and free apps from the Android Market. According to the company, the apps are malware and focused on getting root access to the user’s device (giving them more control over your phone than even you have). Kevin Mahaffey, the CTO of Lookout, a maker of security tools for mobile devices, explained the Android malware discovery in a recent PC World article (emphasis mine):
Posted in Cyber Data Security, Identity Theft Prevention by Identity Theft Speaker John Sileo.
Tags: Android, Android Market, App Store, Applications, Apps, BlackBerry, BlackBerry Security, data security, Droid, Droid Security, Expert, Fraud, Hacking, Hijacking, iPhone, iPhone Security, jail break, jail breaking, Jailbreaking, John Sileo, Lookout, Mobile Phone, safety, Security, Smart Phone, Smartphone, Smartphone Survival Guide